EchoPentest Toolkit
Three surfaces.
One security operating model.
Most breaches succeed through the same three paths: humans, networks, and infrastructure.
The EchoPentest Toolkit is engineered to close those paths with consistent evidence capture, clear prioritisation,
and practical remediation—without enterprise bloat.
Mapping human risk…
Evidence-first reporting
Designed for SMB + regulated teams
Deployable as a service or project
Works with real-world constraints
What you get
Coverage of the three most exploited failure domains, delivered as a coherent toolkit:
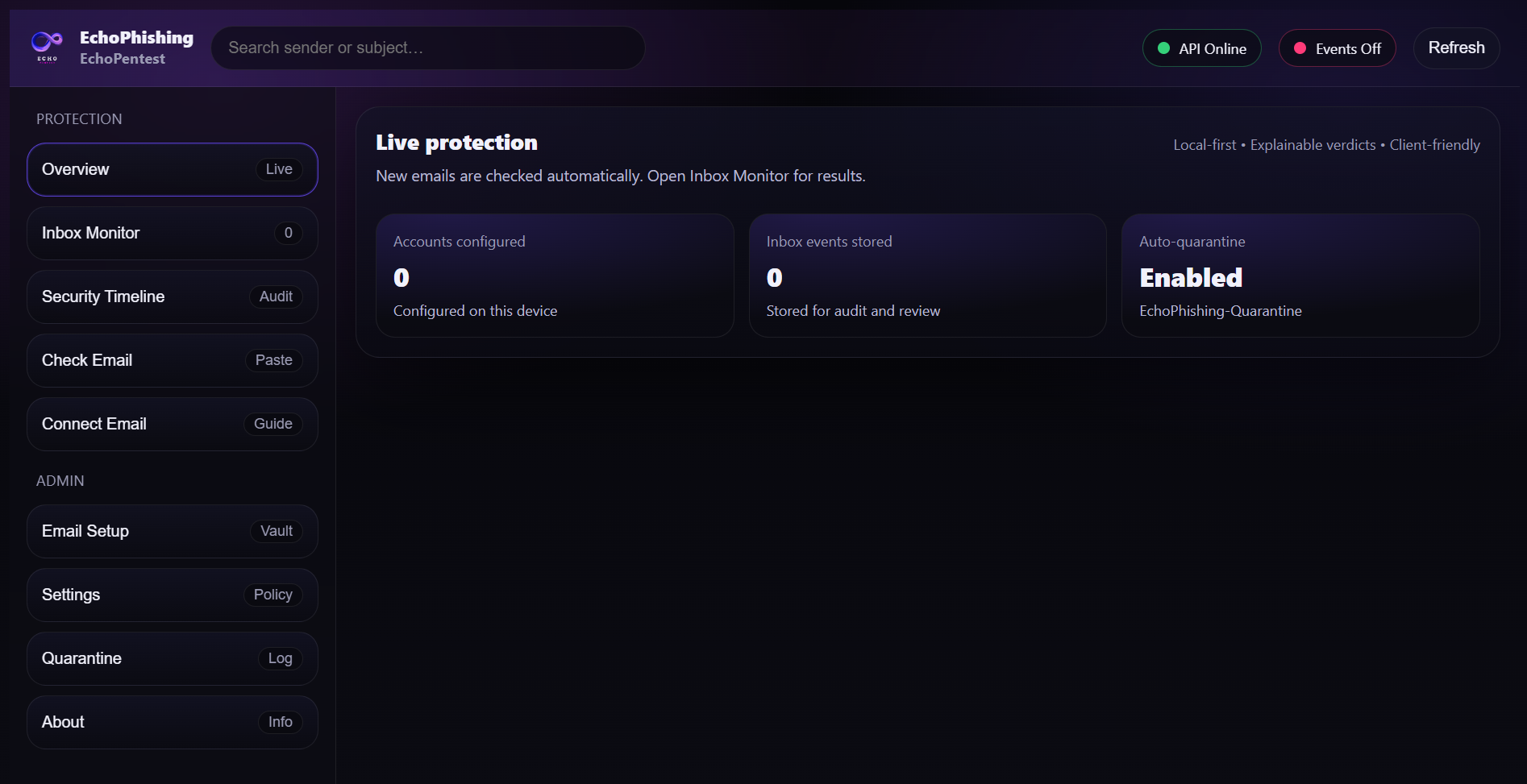
- • Human-layer phishing defence with continuous monitoring options
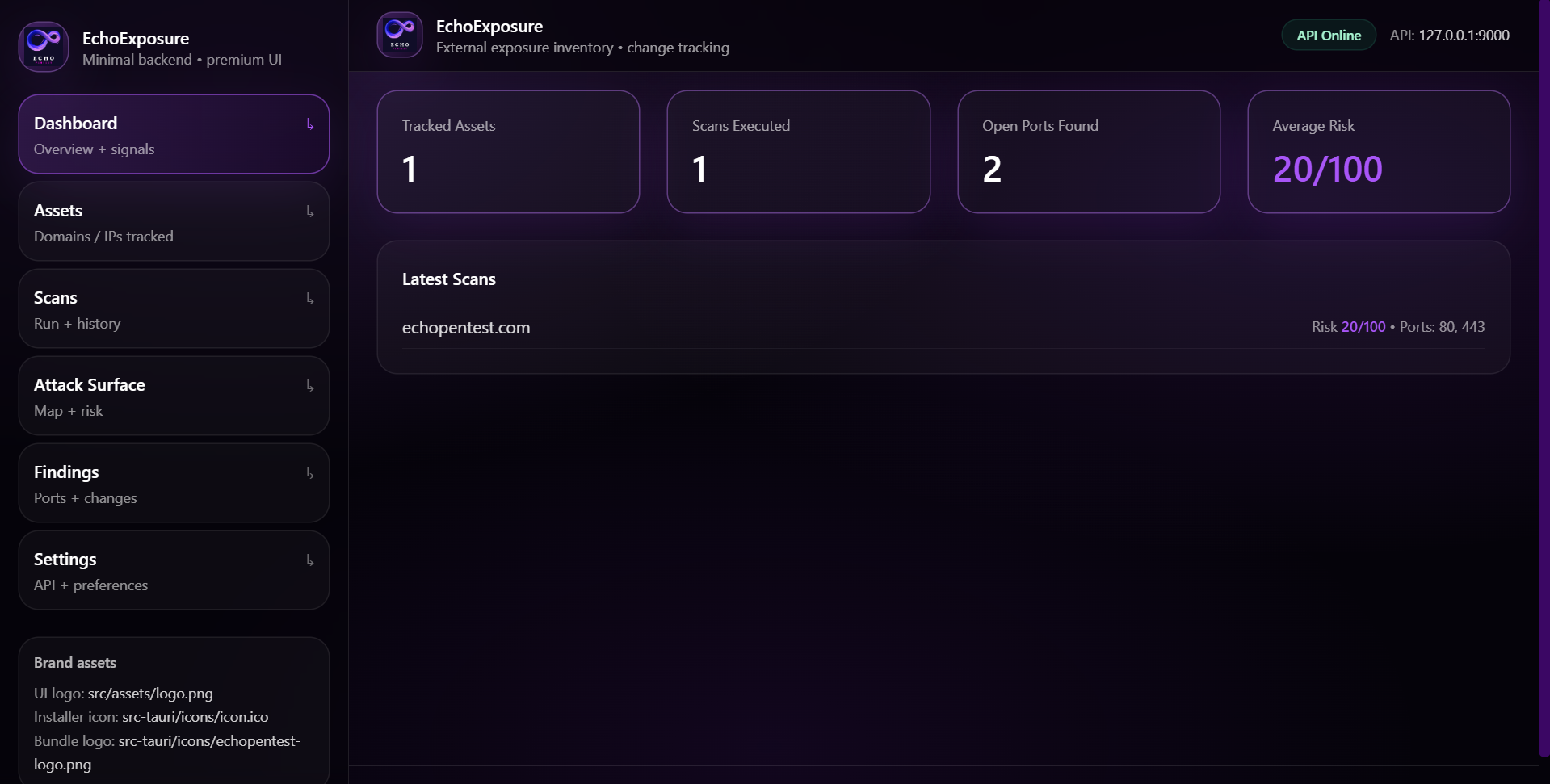
- • Network exposure visibility across assets, ports, services and certificates
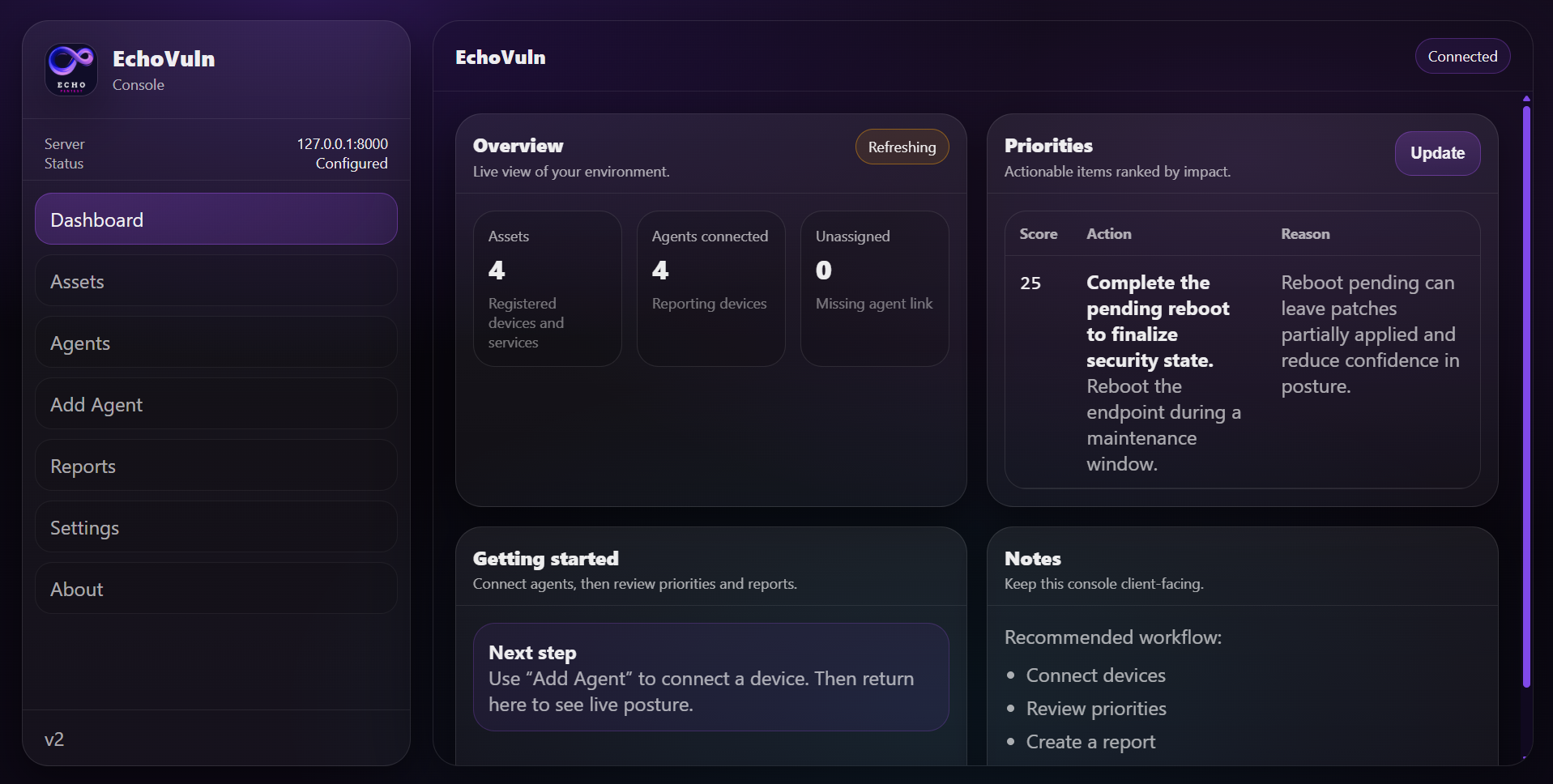
- • Endpoint + infrastructure vulnerability posture with prioritised fixes
- • Executive-ready outputs and engineer-grade evidence
How it’s different
Not “just tools.” Not “just a pentest.” A repeatable protection loop:
- • Baseline → detect drift → prioritise → remediate → verify
- • Findings written as actions, not raw scanner noise
- • Consistent scoring and remediation guidance across products
- • Built for owners and small teams, not only SOCs
Deploy once. Improve continuously.
A single assessment is useful. A repeatable security loop is what stops repeat incidents. The EchoPentest Toolkit can
be delivered as a one-time engagement, or as an ongoing protection program with scheduled checks, reporting and re-testing.
- • Baseline the business: humans, network, infrastructure
- • Prioritise actions that reduce risk fastest
- • Verify fixes and track drift over time
- • Keep documentation audit-ready
Clear scope. Clear deliverables. Clear actions. No theatre.
- Human layer: reduce compromise through inbox risk visibility
- Network layer: remove exposed services and unknown assets
- Infrastructure layer: prioritise patches and hardening that matters
- Verification: confirm fixes and prevent regression